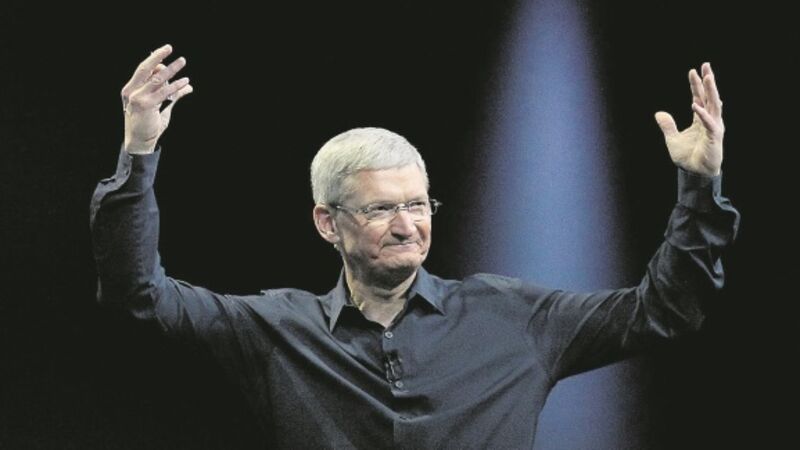
Apple boss Tim Cook was right to stand up to the FBI
The FBI wants Apple to give it the tools to break into the iPhone of the San Bernardino terrorist Syed Farook.
In a brave display on the company home page, Apple boss Tim Cook refused. He was right to say no.
Revoiced
Newsletter
Had a busy week? Sign up for some of the best reads from the week gone by. Selected just for you.












